| Type of paper: | Essay |
| Categories: | CV Profession |
| Pages: | 2 |
| Wordcount: | 419 words |
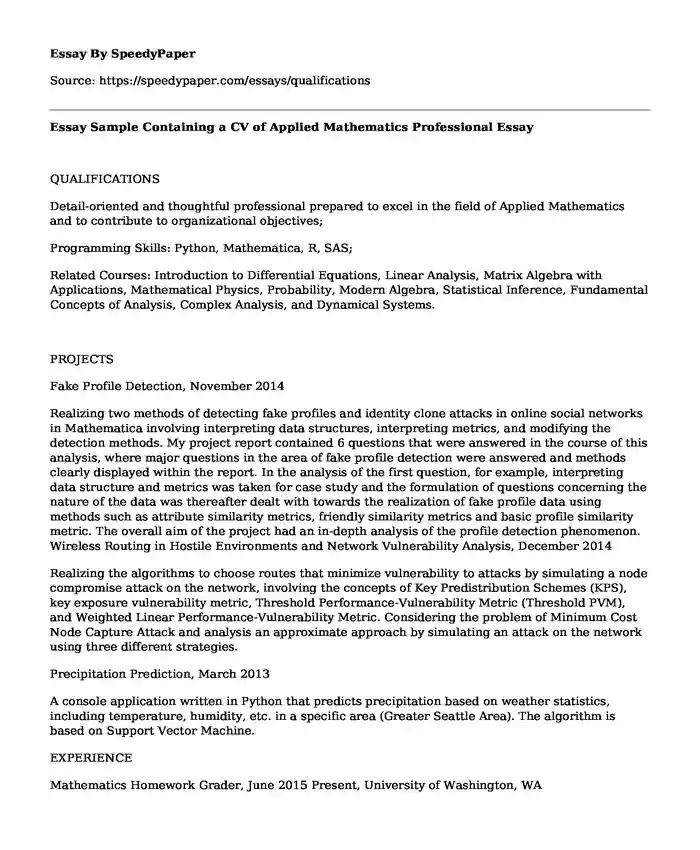
QUALIFICATIONS
Detail-oriented and thoughtful professional prepared to excel in the field of Applied Mathematics and to contribute to organizational objectives;
Programming Skills: Python, Mathematica, R, SAS;
Related Courses: Introduction to Differential Equations, Linear Analysis, Matrix Algebra with Applications, Mathematical Physics, Probability, Modern Algebra, Statistical Inference, Fundamental Concepts of Analysis, Complex Analysis, and Dynamical Systems.
PROJECTS
Fake Profile Detection, November 2014
Realizing two methods of detecting fake profiles and identity clone attacks in online social networks in Mathematica involving interpreting data structures, interpreting metrics, and modifying the detection methods. My project report contained 6 questions that were answered in the course of this analysis, where major questions in the area of fake profile detection were answered and methods clearly displayed within the report. In the analysis of the first question, for example, interpreting data structure and metrics was taken for case study and the formulation of questions concerning the nature of the data was thereafter dealt with towards the realization of fake profile data using methods such as attribute similarity metrics, friendly similarity metrics and basic profile similarity metric. The overall aim of the project had an in-depth analysis of the profile detection phenomenon. Wireless Routing in Hostile Environments and Network Vulnerability Analysis, December 2014
Realizing the algorithms to choose routes that minimize vulnerability to attacks by simulating a node compromise attack on the network, involving the concepts of Key Predistribution Schemes (KPS), key exposure vulnerability metric, Threshold Performance-Vulnerability Metric (Threshold PVM), and Weighted Linear Performance-Vulnerability Metric. Considering the problem of Minimum Cost Node Capture Attack and analysis an approximate approach by simulating an attack on the network using three different strategies.
Precipitation Prediction, March 2013
A console application written in Python that predicts precipitation based on weather statistics, including temperature, humidity, etc. in a specific area (Greater Seattle Area). The algorithm is based on Support Vector Machine.
EXPERIENCE
Mathematics Homework Grader, June 2015 Present, University of Washington, WA
Responsibility: Grading assignments from the courses of Introductory Real Analysis I and II weekly.
Mathematical Contest in Modeling (MCM), February 2014, University of Washington, WA
Problem Description: Analyze the performance of Keep-Right-Except-To-Pass Rule in light and heavy traffic.
Approach: Presented a computerized model (written in Python) by applying the method of Cellular Automation and Monte Carlo Experiments to simulate a series of mobiles actions under the rule restriction. Furthermore, analyzed the influence of the rule on the tradeoff between traffic flow and safety issue regarding to modern freeway traffic, a new model based on the microscopic scale cellular automation model is proposed.
Honor: Honorable Mentions
Cite this page
Essay Sample Containing a CV of Applied Mathematics Professional. (2019, Jul 08). Retrieved from https://speedypaper.net/essays/qualifications
Request Removal
If you are the original author of this essay and no longer wish to have it published on the SpeedyPaper website, please click below to request its removal:
- Battle of Britain - Free Essay in History
- Free Essay Example on Corporate Governance
- Essay Sample: Affirmative Action and Reasons for Regarding Discrimination as Morally Illegitimate
- Free Essay with Reflection Activity: Leadership Self-Assessment
- Classical Conditioning and Operant Conditioning - Free Essay in Psychology
- Missed Nurse Care by Beatrice J. Kalisch, PhD, RN, FAAN
- Essay Sample on Kesterson Reservoir Disaster
Popular categories




